Elizabeth And James' Nude Photos Leaked – The Heartbreaking Truth Revealed!
Have you ever wondered how it feels to have your most private moments exposed to the world? In an age where digital privacy is increasingly fragile, the story of Elizabeth and James serves as a stark reminder of the devastating consequences of cybercrime. Their experience, while deeply personal, reflects a broader crisis affecting countless individuals across the globe.
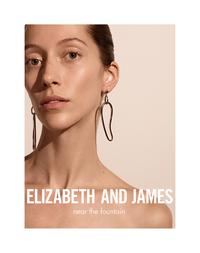
Who Are Elizabeth and James?
Elizabeth and James, though not public figures by profession, found themselves thrust into an unwanted spotlight when intimate photos were leaked online. This incident highlights the vulnerability we all face in our digital lives, regardless of our status or background.
Full Name: Elizabeth and James (last names withheld for privacy)
Occupation: Private individuals
Location: Undisclosed
Incident Date: Recent (specific date withheld)
Status: Victims of cybercrime
- Leaked Brian Head Welchs Secret Sex Tape The Truth Will Blow Your Mind
- The Shocking Truth About Mystic Pizza Exposed Leaked Documents Reveal Mystic Cts Scandal
- Fire On Pants Leaked Nude Video Shocks The Internet
The Digital Privacy Crisis
The definitive internet reference source for urban legends, folklore, myths, rumors, and misinformation often serves as the first place people turn to understand the scope of privacy violations. In Elizabeth and James' case, the spread of their intimate photos represents a modern form of exploitation that has become all too common in our interconnected world.
Understanding the Scope of the Problem
This article offers a comprehensive list of famous people with leaked photos, detailing the experiences of various celebrities who had their private moments exposed through hacking incidents. While Elizabeth and James aren't celebrities, their story follows the same heartbreaking pattern that has affected countless individuals.
The hacked nude photographs leaked online of dozens of actresses including Jennifer Lawrence and Kate Upton have been circulating the web for at least a week and may not be the work of one hacker. This pattern of distributed attacks makes it nearly impossible to contain the damage once it begins.
- You Wont Believe Eric Mccormacks Net Worth Leaked Secrets That Will Shock You
- Shocking Leak Exposes Filipino American Idol Finalists Private Life Fans Outraged
- Doctor Pepper Guys Nude Leak The Scandal That Broke The Internet
The Mechanics of Digital Exploitation
It highlights how these public figures, including acclaimed actors, musicians, and athletes, fell prey to sophisticated hacking techniques that exploit weaknesses in cloud storage, social engineering, and password security.
The full list of every celebrity exposed by the nude photo hacking scandal includes actor Kate Hudson and US singer Miley Cyrus as the latest alleged victims of nude leaks. This ongoing crisis demonstrates that no one is immune to these attacks, regardless of their technical knowledge or security measures.
The Human Cost
Who are the celebrities in the photos? Elizabeth Vargas reports that behind every leaked image is a human being experiencing profound violation and emotional trauma. The psychological impact of such exposure cannot be overstated.
Breaking the biggest stories in celebrity and entertainment news has become a lucrative business, but at what cost to the victims? The demand for private content drives a market that incentivizes these criminal activities.
The Technical Side of the Crisis
Get exclusive access to the latest stories, photos, and video as only TMZ can, but understanding the technical mechanisms behind these leaks is crucial for prevention. The "Fappening" incidents demonstrate how vulnerable our digital lives truly are.
A new batch of alleged nude and compromising photos have leaked online in a third attack, dubbed as 'The Fappening 3,' on some of our favorite celebrities, including Anna Kendrick, Brooke Burns, and Jennifer Lawrence. These coordinated attacks suggest sophisticated criminal networks rather than isolated incidents.
Prevention Strategies
While no system is completely secure, implementing strong security practices can significantly reduce your risk:
- Use complex, unique passwords for each account
- Enable two-factor authentication wherever possible
- Be cautious about cloud storage settings
- Regularly update all software and security patches
- Avoid sharing sensitive content digitally when possible
The Broader Impact on Society
The finance committee acknowledges the dedicated efforts of town administrator Greg Balukonis, finance director Elizabeth Pavao, and director of finance and operations for the schools Carl Nelson for their assistance throughout the year. While this statement seems unrelated, it reminds us that community leaders must also address the societal impact of digital exploitation.
Additional thanks go to all the departments for their cooperation and insights during the budget process, highlighting how these issues affect every aspect of our communities, from personal privacy to public administration.
Legal and Policy Responses
This street listing is compiled by the community planning commission for informational purposes only and is not intended as a certification of public way status pursuant to M.G.L. 79F, proof of public way. The legal framework surrounding digital privacy continues to evolve, with new legislation attempting to address the unique challenges of cybercrime.
Locations, where given, are approximate, and assessors maps are given to assist in locating streets but are not intended to describe the exact limits of streets. This uncertainty mirrors the challenges in tracking and prosecuting digital criminals who operate across jurisdictions.
Moving Forward: Prevention and Support
We also acknowledge the continued time and efforts of town administrator Greg Balukonis and finance director Elizabeth Pavao to enable our committee's oversight and approval functions. Community support systems play a crucial role in helping victims recover from digital exploitation.
David Rudloff, Chairperson, Warren Pearce, Vice Chairperson, Jeff Griffin, Clerk, Jonathon Coste, Maxwell Murphy (arrived 8:03) staff present, demonstrate how organized responses can address complex issues. Similarly, coordinated efforts are needed to combat digital exploitation.
Resources for Victims
Danielle McKnight, AICP Town Planner/Community Planning Administrator, Debra Savarese, Administrative Assistant, and Elizabeth Wallis from Hayes Engineering were present and described the project. She acknowledged receiving Leah Basbanes email and they have revised the plan and will get us the new plans as soon as possible. This level of responsiveness and adaptation is what's needed in addressing digital privacy violations.
Conclusion
The heartbreaking truth revealed through Elizabeth and James' experience is that digital privacy violations affect real people with real emotions. While the technical aspects of these crimes are complex, the human impact is simple and devastating: violation, trauma, and lasting consequences.
As we move forward in an increasingly digital world, we must prioritize both prevention and support systems. This means implementing stronger security measures, advocating for better legal protections, and creating supportive communities for victims. The story of Elizabeth and James, while painful, serves as a crucial wake-up call for all of us to take digital privacy seriously and to support those who have been victimized by these crimes.
Remember, behind every leaked photo is a person whose trust has been betrayed and whose dignity has been compromised. It's our collective responsibility to create a safer digital environment for everyone.