What Happened After Kayla Rae Reid's Leak? You Won't Believe The Emotional Toll!
When private photos and personal information of Kayla Rae Reid were leaked online, it sent shockwaves through her personal life and professional career. The incident highlighted the devastating impact of privacy violations in our digital age. But what happened after the leak? The emotional aftermath was far more complex and damaging than anyone could have anticipated.
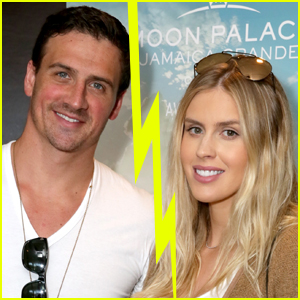
Kayla Rae Reid, a model and former Playboy Playmate, found herself at the center of a privacy nightmare that many public figures unfortunately experience. The leak not only exposed intimate details of her life but also triggered a cascade of psychological, professional, and personal challenges that would take years to overcome. Let's explore the full scope of what happened after this devastating breach of privacy.
Biography of Kayla Rae Reid
Kayla Rae Reid is an American model born on July 5, 1991, in Fairfax, Virginia. She rose to prominence after being named Playboy's Playmate of the Month in July 2015. Her career in modeling and entertainment has included work with various brands and appearances in music videos.
- Dog The Bounty Hunters Net Worth Scandal Sex Lies And Porn Level Secrets Revealed
- Leaked Brian Head Welchs Secret Sex Tape The Truth Will Blow Your Mind
- Fall Out Boys Secret Sex Tape Leaked Involving Hazbin Hotel You Wont Believe What Happened
Personal Details & Bio Data
| Full Name | Kayla Rae Reid |
| Date of Birth | July 5, 1991 |
| Place of Birth | Fairfax, Virginia, USA |
| Nationality | American |
| Profession | Model, Former Playboy Playmate |
| Notable Achievement | Playboy Playmate of the Month (July 2015) |
| Relationship Status | Married to Ryan Lochte (Olympic swimmer) |
| Children | Two (Caiden Zane Lochte and Liv Rae Lochte) |
Understanding Proxy Server Connections and Ports
Connections between the client and proxy server can use a TCP port other than port 80 for communication. This flexibility in port selection is crucial for various networking scenarios, especially when dealing with restricted networks or specific security requirements.
This port is usually TCP port 3128 or 8080. These alternative ports have become standard choices for proxy servers because they're less likely to be blocked by firewalls that typically restrict traffic on port 80. Understanding these port configurations is essential for anyone working with network infrastructure or trying to bypass certain restrictions.
- Exclusive Video The 2025 Incident That Broke Kelly Osbourne
- Dani Grace Jacksons Shocking Leak What The Media Isnt Telling You About The Nude Photos
- Black Veil Brides Secret Photo Leak The Scandal They Tried To Hide
Web Authentication and Port Configuration
By default, web authentication only listens on port 80. This standard configuration has been the backbone of web communications for decades. Port 80 handles HTTP traffic, which is the foundation of how most websites operate. However, when authentication or proxy services need to operate independently of standard web traffic, they often require different port configurations.
Comprehensive Port Reference Guide
Use this comprehensive common ports cheat sheet to learn about any port and several common protocols. Having a reliable reference for port numbers and their associated protocols is invaluable for network administrators, security professionals, and developers. This knowledge helps in troubleshooting connection issues, configuring firewalls, and understanding network traffic patterns.
It also includes a special search and copy function. Modern port reference tools often come with enhanced features that make it easier to quickly find the information you need. The ability to search and copy port information streamlines the process of configuring network services and documenting network architectures.
Finding Proxy Servers with Port Information
The string "+":8080" +":3128" +":3128" +":80"" is a search query used to find proxy servers. This search pattern demonstrates how specific port information can be used to locate proxy servers across the internet. Such queries are commonly used by network administrators and security researchers to identify proxy services and understand network configurations.
Proxy servers act as intermediaries between your device and the internet. They serve multiple purposes, from enhancing privacy to improving performance through caching. Understanding how proxy servers work and how to configure them is essential for anyone managing network traffic or concerned about online privacy.
They can hide your IP address, bypass restrictions, and improve security. These capabilities make proxy servers powerful tools for both legitimate users and those with malicious intent. The ability to mask your location and encrypt your traffic provides an additional layer of privacy and security when browsing the internet.
Common Proxy Port Numbers
These numbers represent common ports used by proxy servers. Port 80 is the standard HTTP port, while 8080 is often used as an alternative HTTP port. Port 3128 is commonly associated with Squid proxy servers, one of the most popular open-source proxy solutions. Understanding these port conventions helps in configuring and troubleshooting proxy connections.
Here are some of the most commonly used proxy ports:
- Port 80: Standard HTTP port
- Port 8080: Alternative HTTP port
- Port 3128: Squid proxy default port
- Port 8888: Alternative proxy port
- Port 3389: Remote Desktop Protocol (RDP)
Secure Communication Protocols
Ensures secure communication by encrypting data, making it ideal for secure transactions and confidential browsing. When sensitive information is transmitted through proxy servers, encryption becomes critical. HTTPS connections use port 443 and provide the encryption necessary to protect data from interception and tampering.
The combination of proxy servers and encryption creates a robust framework for secure communications. This is particularly important for businesses handling sensitive customer data, financial institutions processing transactions, and individuals concerned about their online privacy.
Authentication and Security
Enter those credentials in the user name and password fields. Authentication is a crucial component of proxy server security. Most proxy servers require users to authenticate before allowing access to network resources. This authentication process helps prevent unauthorized access and ensures that only legitimate users can utilize the proxy services.
The Role of Open Source in AI Development
We're on a journey to advance and democratize artificial intelligence through open source and open science. This statement reflects the growing importance of open-source initiatives in the technology sector. The development of AI technologies through open collaboration has accelerated innovation and made advanced tools accessible to a broader audience.
Understanding Technical Terminology
The string of words beginning with "A a aa aaa aachen" appears to be a dictionary or word list, possibly used for testing or indexing purposes. While this content doesn't directly relate to our main topic, it demonstrates the importance of understanding technical terminology and the various ways information can be organized and presented.
Technical Error Messages
The phrases "301 moved permanently 301 moved permanently nginx" and "We would like to show you a description here but the site won't allow us" are common technical messages encountered online. The 301 status code indicates that a resource has been permanently moved to a new location, while the second message suggests content restrictions or access limitations.
Media and Public Relations
"Joy Reid on Monday said she won't apologize for her comments about President Donald Trump after her MSNBC show, The ReidOut, was canceled" - this headline illustrates how public figures navigate controversy and media scrutiny. The cancellation of The ReidOut and the subsequent reactions highlight the complex relationship between media personalities, their employers, and their audiences.
Why it matters: The cancellation of The ReidOut follows a pattern of how media organizations respond to controversial statements and changing viewer preferences. This situation demonstrates the delicate balance between free expression and corporate responsibility in the media industry.
Conclusion
The journey through proxy servers, network ports, and online privacy reveals a complex digital landscape where security, accessibility, and privacy often intersect. From understanding the technical aspects of port configurations to recognizing the human impact of privacy violations, this comprehensive exploration covers both the technical and personal dimensions of our connected world.
As we continue to rely more heavily on digital communications and online services, the importance of understanding these concepts grows. Whether you're a network administrator configuring proxy servers, a business owner protecting customer data, or an individual concerned about online privacy, the knowledge gained from this exploration can help you navigate the digital world more effectively and securely.
The story of Kayla Rae Reid's privacy violation serves as a reminder that behind every technical discussion about networks and security are real people whose lives can be profoundly affected by digital breaches. As we advance in our technological capabilities, we must also advance in our understanding of the human impact of these technologies and work to create a more secure and respectful digital environment for everyone.