The Shocking Secret To Switch Back To Personal Account And Hide Your Sex Tapes From Hackers!
Have you ever wondered how to protect your most private digital content from prying eyes? In today's hyper-connected world, where data breaches and hacking scandals make headlines daily, safeguarding your personal information has become more critical than ever. From celebrity sex tapes being leaked to ordinary users falling victim to cybercrime, the need for robust digital security measures cannot be overstated. This comprehensive guide will reveal the shocking truth about protecting your most sensitive content while navigating the complex landscape of online privacy.
Understanding What Makes Content "Shocking"
The meaning of shocking is extremely startling, distressing, or offensive. When we encounter something shocking, it typically causes intense surprise, disgust, horror, or offense, often because it's unexpected or unconventional. In the digital age, shocking content can range from disturbing news stories to intimate personal materials falling into the wrong hands.
How to use shocking in a sentence? Consider this example: "The revelation of the leaked celebrity tapes was truly shocking to fans worldwide." This demonstrates how the term applies to events that cause moral outrage or violate societal norms. Similarly, you can say that something is shocking if you think that it is morally wrong or ethically questionable.
- Air Belgiums Massive Leak Secret Flight Routes And Crew Scandals Exposed
- Michael Coles Net Worth Secrets Exposed What He Doesnt Want You To Know
- You Wont Believe The Secret Sex Scandals Happening At Ace Hotel Palm Springs
The Digital Privacy Crisis
Extremely bad or unpleasant, or of very low quality describes many of today's privacy protection measures. Despite technological advancements, our personal data remains vulnerable to various threats. Shocking synonyms include appalling, dreadful, and terrible – all terms that aptly describe the current state of digital privacy.
It is shocking that nothing was said about major data breaches until after millions of users were affected. According to cybersecurity experts, the average cost of a data breach reached $4.45 million in 2023, yet many individuals remain unaware of the risks they face daily.
Celebrity Scandals and Privacy Violations
The entertainment industry has witnessed numerous shocking incidents involving private content leaks. From celebrity scandals to high-profile divorces, the public's fascination with intimate details has created a dangerous environment for privacy. Anonymous, an international collective of hacktivists, has orchestrated cyberattacks against various targets, including celebrities and corporations, exposing sensitive information to the world.
- You Wont Believe Joe Santagatos Secret Net Worth Leak
- Adam Kinzingers Net Worth Leaked The Shocking Financial Secrets They Buried
- The Jaw Dropping Truth About Michael Bublés Hidden Millions Leaked
Her first husband Ojan Noja recorded the couple having sex, and now his business partner threatens to unveil the film for the world to see. As we are waiting for this, we present you 12 most shocking celebrity sex tapes that made headlines globally. These incidents serve as stark reminders of how vulnerable our private content can be in the digital age.
Protecting Your Digital Privacy
Here are the best places I've found to hide sex toys, but the real question is: how do you protect your digital content? Just please don't tell my kids! The same principles that apply to physical privacy can be adapted for digital security.
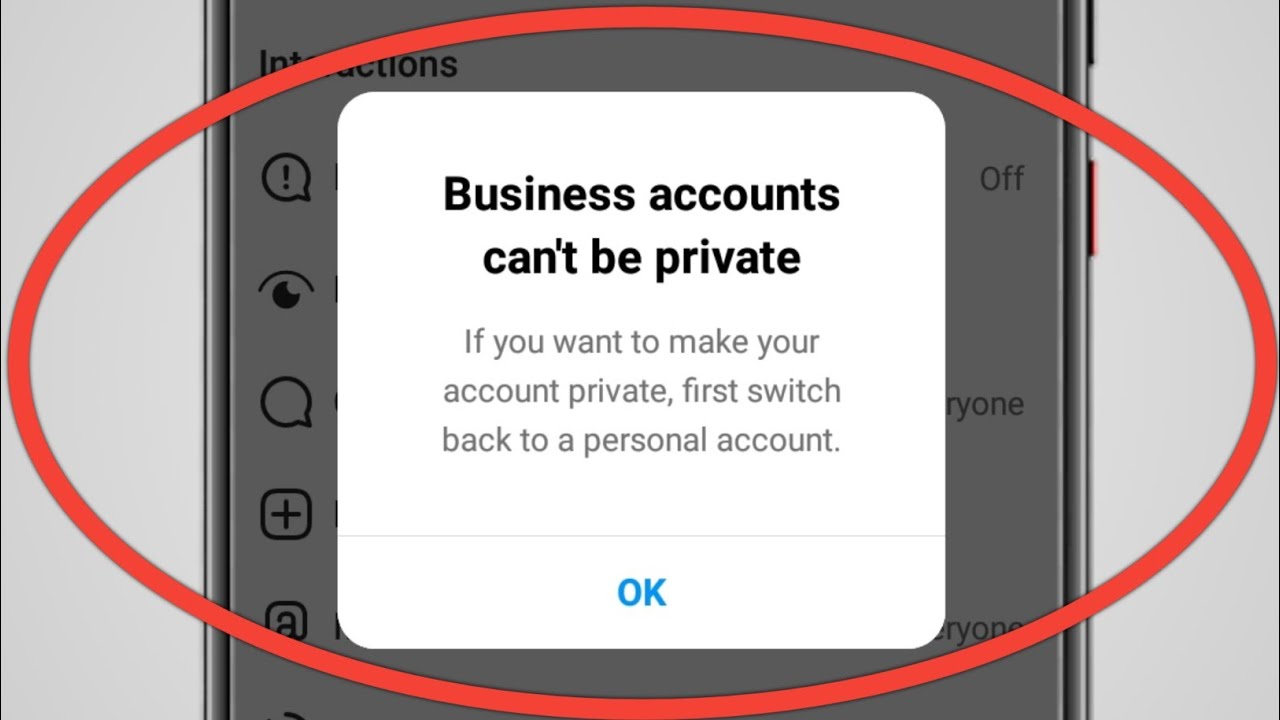
The Shocking Secret: Switch back to a personal account and implement multiple layers of security. Here's how:
- Use Strong Passwords: Create complex passwords that combine letters, numbers, and special characters
- Enable Two-Factor Authentication: Add an extra layer of security beyond just passwords
- Regular Account Audits: Review your connected devices and active sessions frequently
- Privacy Settings Optimization: Adjust your social media and cloud storage settings to maximum privacy
Advanced Protection Techniques
But I'm going to let you in on a little secret: hiding your digital content requires more sophisticated strategies than most people realize. Here are proven methods to protect your most sensitive files:
Encryption Methods
Encryption transforms your data into unreadable code that only you can access. Use tools like VeraCrypt or BitLocker to encrypt entire drives containing sensitive content. For individual files, consider using AxCrypt or similar encryption software.
Cloud Storage Security
When using cloud services, implement these protective measures:
- Use end-to-end encrypted cloud storage services
- Create separate, anonymous accounts for sensitive content
- Enable two-factor authentication on all cloud services
- Regularly review and revoke access permissions
IP Address Protection
How to hide your IP address in an age where it's common to read headlines about hackers breaking into company and personal networks? Use a reliable VPN service that doesn't log your activity. This masks your real location and makes it harder for hackers to target you specifically.
Common Mistakes to Avoid
Little did I know that, in several short years, a sea change in the digital landscape would create new vulnerabilities. Here are common mistakes that leave your content exposed:
- Using Public Wi-Fi for Sensitive Activities: Public networks are prime targets for hackers
- Weak Password Practices: Reusing passwords across multiple accounts
- Ignoring Software Updates: Outdated software contains known vulnerabilities
- Over-sharing on Social Media: Revealing too much personal information
Emergency Response Plan
Here are a few ways to go about it if your content is compromised:
- Immediate Action: Change all passwords and enable two-factor authentication
- Legal Steps: Consult with a lawyer about your rights and potential actions
- Platform Reporting: Report the content to the hosting platform
- Reputation Management: Work with professionals to minimize damage
Just to be clear, we're talking about your digital porn collection here, but these principles apply to any sensitive content you want to protect.
Technical Implementation Guide
To effectively hide your sensitive content from hackers, follow this comprehensive approach:
Digital Organization
Create a logical file structure that makes sense to you but appears innocuous to others. Use misleading folder names and consider creating decoy folders with less sensitive content.
Backup Strategies
Implement the 3-2-1 backup rule: three copies of your data, on two different media types, with one copy stored off-site. Ensure all backups are encrypted and password-protected.
Access Control
Set up strict access controls for all your accounts and devices. Use biometric authentication where available and regularly review who has access to your accounts.
The Future of Digital Privacy
The latest news and headlines from Yahoo News and other sources indicate that privacy concerns will only intensify. As technology advances, so do the methods used by those seeking to exploit it. Staying informed about the latest security threats and protection methods is crucial.
Conclusion
Protecting your most sensitive digital content requires vigilance, knowledge, and the right tools. By implementing the strategies outlined in this guide, you can significantly reduce your risk of becoming a victim of privacy violations. Remember that digital security is an ongoing process, not a one-time setup.
The shocking reality is that our digital footprints are permanent, but with proper precautions, we can control who accesses our most private content. Stay informed, stay protected, and maintain your digital privacy in an increasingly connected world.