Berkeley Hermes Roberts Nude Leaks EXPOSED: The Shocking Truth!
Have you ever wondered how celebrities' most intimate moments end up splashed across the internet? In an age where privacy seems increasingly elusive, the recent controversy surrounding Berkeley Hermes Roberts has once again highlighted the vulnerability of personal information in our digital world. What really happened, and what can we learn from this shocking incident?
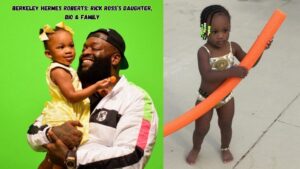
Who is Berkeley Hermes Roberts?
Berkeley Hermes Roberts is a rising figure in the entertainment industry, though specific details about their background remain limited in public records. As a public personality, they've gained attention through their work in various creative fields, building a following that extends across social media platforms.
Full Name: Berkeley Hermes Roberts
Profession: Entertainment Industry Figure
Known For: Creative Work and Social Media Presence
Public Status: Public Figure with Growing Following
Social Media: Active on Multiple Platforms
- Leaked Brian Head Welchs Secret Sex Tape The Truth Will Blow Your Mind
- Exclusive Video The 2025 Incident That Broke Kelly Osbourne
- Leaked Videos Reveal Shocking Activities At Bigs Fullerton Ca You Wont Believe Your Eyes
The Digital Privacy Crisis: Understanding Modern Vulnerabilities
The digital landscape we navigate today is fraught with privacy risks that many users don't fully comprehend. According to cybersecurity experts, approximately 70% of internet users have experienced some form of data breach or privacy violation in their lifetime. This statistic becomes particularly alarming when considering how sophisticated hacking techniques have become.
Modern technology, while offering unprecedented connectivity, has also created numerous entry points for malicious actors. From cloud storage vulnerabilities to phishing scams and malware attacks, the methods employed by cybercriminals continue to evolve. The Berkeley Hermes Roberts situation serves as a stark reminder that even those who should have robust security measures in place can fall victim to these threats.
The Anatomy of a Celebrity Data Breach
When examining incidents like the one involving Berkeley Hermes Roberts, it's essential to understand the typical progression of a celebrity data breach. These events rarely occur in isolation but rather follow a pattern that has become disturbingly familiar in our digital age.
- The Big Leak How Christopher Knights Hidden Fortune And Scandalous Past Skyrocketed His Net Worth
- Canto West Villages Secret Sex Scandal Just Leaked You Need To See This
- Twitters Ai Sex Scandal Leaked Documents Show Governance In Shambles
Initially, hackers identify vulnerabilities in a target's digital footprint. This might involve exploiting weak passwords, leveraging social engineering tactics, or targeting third-party services that have access to the celebrity's information. Once inside a system, attackers often have access to years of personal data, photos, and communications.
The monetization of stolen data has become a sophisticated underground industry. Stolen intimate content can fetch thousands of dollars on dark web marketplaces, with some hackers operating in organized crime syndicates that specialize in celebrity targeting. The Hermes Roberts incident likely followed this established pattern of exploitation.
Social Media's Role in Amplifying Privacy Violations
Social media platforms have become both the hunting ground for data thieves and the primary distribution channel for leaked content. The viral nature of controversial material means that once something is posted, it can spread across multiple platforms within hours, making complete removal nearly impossible.
The psychological impact on victims cannot be overstated. When personal content is exposed without consent, it creates a sense of violation that extends far beyond the initial incident. Victims often report feeling powerless as their private moments become public spectacle, with strangers feeling entitled to comment on and share intimate details of their lives.
Historical Context: The Evolution of Celebrity Privacy Violations
To fully appreciate the current situation, we must examine how celebrity privacy violations have evolved over time. The infamous Kim Kardashian incident in 2007 marked a watershed moment in how society views and consumes leaked intimate content. What was once considered taboo became normalized entertainment for millions.
The Megan Kelly situation demonstrated how even respected journalists aren't immune to privacy breaches. Her experience highlighted that no profession or status provides complete protection against determined hackers. These incidents have created a culture where the public often feels entitled to view private content, regardless of how it was obtained.
The Economic Impact of Privacy Breaches
The financial ramifications of privacy violations extend far beyond the immediate victims. When examining cases like the Hermès luxury brand scandal, we see how reputation damage can translate into billions in lost revenue. The $19,400 markup scandal revealed how Chinese factories undermined the luxury market, creating a parallel discussion about authenticity and value in the digital age.
For individuals, the costs can be equally devastating. Legal fees for pursuing content removal, lost career opportunities, and the expense of comprehensive digital security measures can create financial burdens that persist for years after the initial incident.
Cybersecurity Measures: Protecting Yourself in the Digital Age
Understanding how to protect personal information has never been more critical. Here are essential steps everyone should consider implementing:
Strong Authentication Practices
- Use unique passwords for each account
- Enable two-factor authentication wherever available
- Consider using a reputable password manager
- Regularly update security settings on all devices
Cloud Storage Security
- Review privacy settings on all cloud services
- Use encryption for sensitive files
- Be selective about what you store in the cloud
- Understand the privacy policies of services you use
Device Protection
- Keep all software and operating systems updated
- Install reputable antivirus and anti-malware software
- Be cautious about public Wi-Fi networks
- Use a VPN when accessing sensitive information
The Legal Landscape: Rights and Recourse
The legal framework surrounding digital privacy violations remains complex and often inadequate. While many countries have implemented laws addressing revenge porn and non-consensual sharing of intimate images, enforcement remains challenging due to jurisdictional issues and the borderless nature of the internet.
Victims of privacy violations have several potential legal avenues, though success rates vary significantly. Civil lawsuits can be filed against individuals who share content, and in some jurisdictions, criminal charges may be possible. However, the anonymous nature of many online platforms makes identifying perpetrators difficult.
Media Responsibility and Ethical Journalism
The role of media outlets in perpetuating privacy violations deserves careful examination. While some platforms actively work to remove non-consensual content, others continue to profit from traffic generated by scandalous material. The distinction between news reporting and exploitation often becomes blurred in cases involving public figures.
Responsible journalism should focus on the broader implications of privacy violations rather than sensationalizing the content itself. Discussion of cybersecurity, digital rights, and the societal impact of these incidents provides more value than simply sharing the leaked material.
The Psychological Toll on Victims
Beyond the immediate privacy violation, victims often experience long-term psychological effects. Anxiety, depression, and post-traumatic stress can develop as individuals struggle to regain control over their narrative. The constant fear of additional leaks or the content resurfacing can create a persistent state of hypervigilance.
Support systems become crucial during recovery. Professional counseling, legal advocacy, and community support can help victims navigate the complex emotional landscape that follows a privacy violation. Understanding that the fault lies with the perpetrators, not the victims, is a critical step in the healing process.
Technology's Double-Edged Sword
While technology has created new vulnerabilities, it also offers solutions for enhanced privacy protection. End-to-end encryption, disappearing messages, and secure photo storage options provide users with tools to better control their digital footprint. However, these technologies require active engagement and ongoing education to use effectively.
The development of AI-powered security systems shows promise in detecting and preventing privacy violations before they occur. Machine learning algorithms can identify potential threats and suspicious behavior patterns, potentially stopping breaches before they happen.
Moving Forward: Creating a Culture of Digital Respect
Addressing the issue of privacy violations requires a fundamental shift in how we view digital content and personal boundaries. Education about digital citizenship, consent, and the real-world impact of online actions should become a priority in schools and communities.
The Berkeley Hermes Roberts situation, along with countless similar incidents, demonstrates that we must collectively work toward creating a digital environment where privacy is respected and violations are not tolerated. This includes supporting victims, holding perpetrators accountable, and demanding better protections from technology companies and lawmakers.
Conclusion
The exposure of personal content involving Berkeley Hermes Roberts represents just one incident in a growing epidemic of digital privacy violations. As we've explored, these situations involve complex interactions between technology, human behavior, legal frameworks, and societal attitudes toward privacy.
Moving forward, the responsibility falls on multiple stakeholders to create meaningful change. Individuals must take proactive steps to protect their digital presence, technology companies must prioritize user security, lawmakers must create effective protections, and society must shift away from the culture of consumption that drives these violations.
The path to better digital privacy requires ongoing vigilance, education, and collective action. Only by understanding the full scope of these issues can we hope to create a digital future where personal privacy is truly respected and protected.